Hybrid cloud adoption continues to accelerate as organizations pursue agility, cost optimization, and resilience. By combining on-premises systems with public cloud services, hybrid architectures deliver flexibility — but they also expand the attack surface. Attackers target hybrid environments because they expose more assets, introduce complex trust boundaries, and rely on diverse tooling and processes.
A focused threat landscape analysis shows a rise in attacks that exploit misconfigurations, identity weaknesses, API vulnerabilities, and supply-chain gaps. These hybrid cloud security threats are amplified by rapid developer-driven change, automation, and third-party dependencies. This article will walk through mapping the threat landscape, identifying emerging security risks, explaining operational challenges, reviewing security trends, recommending risk management strategies, and outlining how organizations should prepare for the future of multi-environment security.
Stay Ahead of Emerging Threats
Download our comprehensive 2023 Hybrid Cloud Threat Report to understand the latest attack vectors and mitigation strategies.
Download Threat Report
Mapping the Threat Landscape for Hybrid infrastructure Environments
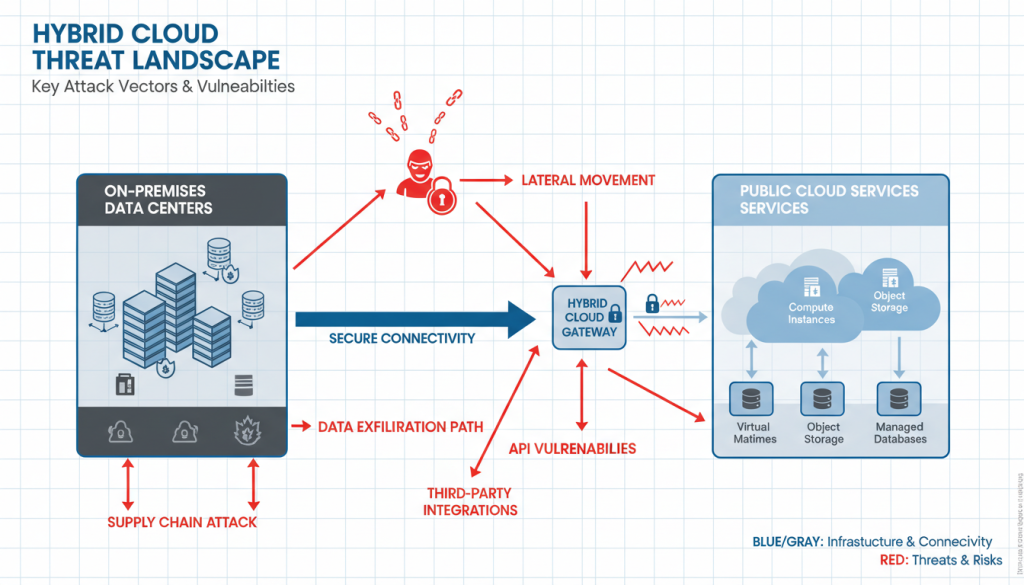
Figure 1: Hybrid cloud security threat landscape showing common attack vectors
Threat Landscape Analysis: Assets, Attack Surfaces, and Hybrid Complexity
Mixed cloud environment environments combine many asset types: virtual machines, containers, serverless functions, APIs, identity providers, on-premises appliances, and data stores. Each asset class creates unique vulnerabilities and interdependencies that attackers can exploit.
Key dimensions to include in a threat landscape analysis:
- Assets: data (structured/unstructured), identity credentials, keys, configuration templates, CI/CD pipelines.
- Attack surfaces: public APIs, management consoles, misconfigured storage buckets, VPNs, EDR telemetry collectors, and east-west network paths between cloud and on-premises.
- Complexity: multiple cloud providers (multi-cloud), legacy on-premises systems, and third-party SaaS integrations increase risk due to inconsistent controls and divergent logging.
Common Attack Vectors in Multi-environment Security
Attackers targeting hybrid infrastructure environments typically exploit several common vectors:
- Data exfiltration: attackers find misconfigured storage or leaked keys and move data to external endpoints. Publicly exposed S3/Blob containers remain a frequent cause of breaches.
- Lateral movement: once inside a workload or network segment, adversaries exploit over-privileged accounts and weak network segmentation to pivot to critical systems.
- API exploitation: insecure APIs and insufficient rate-limiting enable abuse of cloud services, privilege elevation, and data access.
- Supply-chain attacks: compromised open-source libraries or CI/CD toolchains can introduce backdoors into production systems.
Hybrid Cloud Security Threats Tied to Cloud-Native and On-Prem Integrations
Hybrid environments mix cloud-native technologies (Kubernetes, serverless) with legacy on-premises platforms. Attackers exploit the weakest link:
- Weakly isolated Kubernetes namespaces or container runtimes
- Insecure network tunnels connecting on-premises and cloud workloads
- Misaligned identity and policy enforcement across domains
Transitioning workloads to the cloud without rethinking security controls often results in inherited or new vulnerabilities that attackers can exploit.
Emerging Security Risks Specific to Combined cloud
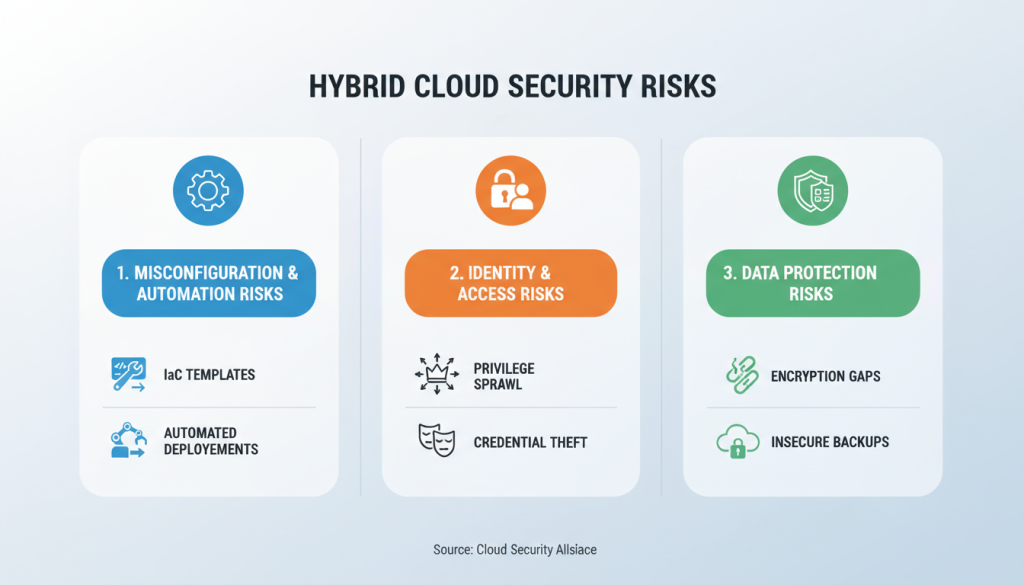
Figure 2: Key emerging security risks in hybrid cloud environments
Misconfiguration and Automation Gaps as an Emerging Security Risk
As organizations scale, automated provisioning (Infrastructure as Code) accelerates. But automation can propagate misconfigurations at scale:
- Incorrect IAM policies embedded in Terraform or ARM templates
- Unsecured default settings in managed services
- CI/CD pipelines that deploy changes without automated security gates
A single misconfigured template can expose thousands of resources. Gartner warned that through 2025, "99% of cloud security failures will be the customer's fault" — mainly stemming from misconfiguration and poor governance.
A bank using IaC to spin up test clusters accidentally left a storage container unencrypted and publicly readable. Automation then replicated that configuration across environments, creating widespread exposure.
Identity and Access Risks: Privilege Sprawl, Identity Federation, and Credential Theft
Identity is the new perimeter in multi-environment security. Emerging risks include:
- Privilege sprawl: legacy accounts and broad roles accumulate permissions over time.
- Identity federation complexity: SSO/SAML/OIDC mistakes can create trust chains attackers abuse.
- Credential theft: exposed secrets in code repositories or leakages from dev machines.
Data Protection Risks: Multi-tenant Exposure, Encryption Gaps, and Insecure Backups
Data protection risks in hybrid infrastructures include:
- Multi-tenant exposure: poorly isolated tenants in public clouds can leak metadata or data across customers.
- Encryption gaps: data at rest or in transit may not be properly encrypted or keys may be mismanaged.
- Insecure backups: backups stored in accessible buckets or without immutability protections enable data loss or ransomware.
According to the IBM 2023 Cost of a Data Breach Report, compromised credentials and cloud misconfigurations were significant root causes of costly breaches, with the average breach cost at $4.45 million.
Cloud Security Challenges and Operational Impacts

Figure 3: Operational cloud security challenges in hybrid environments
Visibility and Monitoring Challenges Across Hybrid Environments
One of the hardest operational impacts is lack of visibility. Data and telemetry are fragmented across providers and on-premises systems:
- Centralizing logs and enabling full-stack observability is nontrivial.
- Blind spots allow attackers to persist undetected.
- Alert fatigue from noisy signals undermines SOC effectiveness.
Practical mitigation: invest in a centralized SIEM/Cloud-native security analytics with normalized telemetry and context-aware alerts.
Compliance and Governance Complexities: Regulatory Overlap and Auditability
Combined clouds often cross regulatory domains (e.g., GDPR, HIPAA, PCI DSS). Challenges include:
- Mapping controls across cloud and on-premises systems
- Maintaining data residency and sovereignty
- Proving auditability during compliance checks
A multinational enterprise using US-based SaaS for European customer data must carefully document processing agreements and technical controls to maintain compliance with GDPR while operating in a hybrid cloud environment.
People and Process Issues: Skills Gaps, DevSecOps Adoption, and Change Management
People and process challenges are persistent in securing hybrid setup environments:
- Security skills shortages slow adoption of modern controls.
- DevSecOps cultural change is required to integrate security into fast pipelines.
- Change management: frequent infrastructure changes require governance to avoid drift.
Organizations should address these challenges through training, security champions in dev teams, and clear guardrails in CI/CD pipelines.
Assess Your Mixed cloud environment Security Posture
Request a comprehensive security assessment to identify gaps in your multi-environment environment and receive tailored recommendations.
Request Security Assessment
Cloud Security Trends Shaping Hybrid Defenses

Figure 4: Key cloud security trends shaping hybrid cloud defenses
Shift-Left and Infrastructure-as-Code Trends and Their Security Implications
Shift-left practices embed security earlier in development:
- Scanning IaC templates for misconfigurations
- Testing container images in CI
- Policy-as-Code to enforce security gates
Benefits include early detection and fewer change rollbacks. However, security rules must be integrated without slowing delivery to be effective in hybrid infrastructure environments.
Zero Trust, SASE, and Other Architectural Trends for Combined cloud Security
Architectural trends reshaping hybrid defenses:
- Zero Trust: assume no implicit trust — verify identity, context, and device posture for every access decision.
- SASE (Secure Access Service Edge): converges networking and security services to secure distributed users and workloads.
- Service Meshes: provide observability and mTLS between microservices.
"Adopt least privilege, assume breach, and verify continuously" — a useful mantra for hybrid setup security.
Use of Automation, AI/ML, and Advanced Analytics in Threat Detection and Response
Automation and AI/ML bring scale to hybrid cloud security:
- Automated detection of anomalous access patterns
- Automated remediation of misconfigurations (with guardrails)
- Orchestrated response playbooks that reduce mean time to respond (MTTR)
Caveat: ML models require quality data and continuous tuning to avoid false positives/negatives in hybrid environments.
Mixed cloud environment Risk Management and Mitigation Strategies
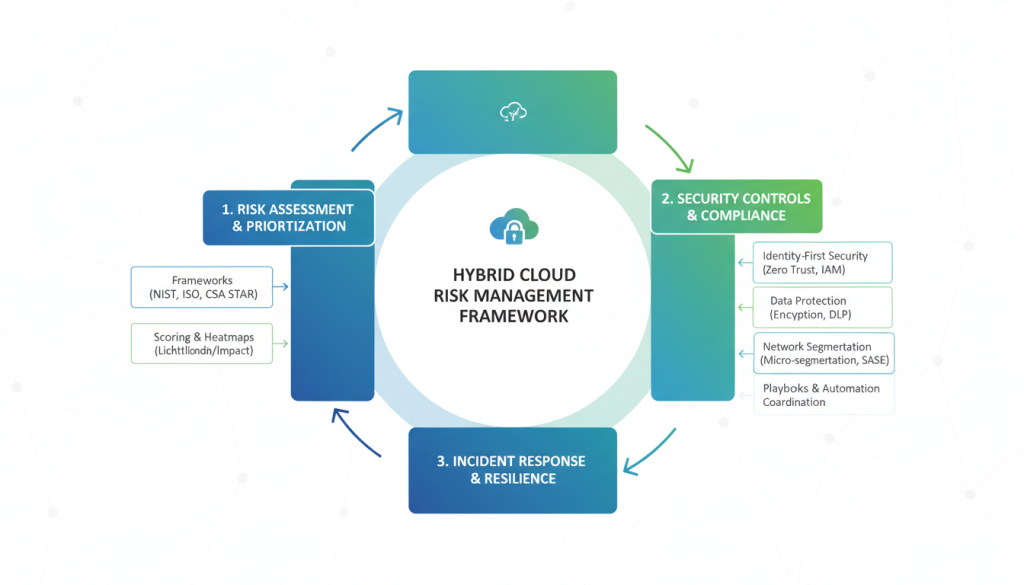
Figure 5: Comprehensive framework for hybrid cloud risk management
Risk Assessment and Prioritization: Frameworks, Continuous Threat Landscape Analysis, and Scoring
Adopt a continuous risk assessment approach for combined cloud security:
- Use recognized frameworks (NIST CSF, ISO 27001, CIS Controls) to map controls.
- Perform threat modeling and attack path analysis regularly.
- Implement risk scoring that factors likely impact and exploitability.
Example: prioritize remediation for public-facing control plane misconfigurations over low-impact internal alerts.
Controls and Best Practices: Identity-First Security, Encryption, Network Segmentation, and Secure CI/CD
Core controls for hybrid setup risk reduction:
Identity & Access Management (IAM)
- Implement least privilege and role-based access
- Deploy conditional access policies
- Enforce multi-factor authentication
Encryption
- Ensure encryption in transit and at rest
- Use customer-managed keys where appropriate
- Implement key rotation policies
Network Segmentation
- Apply microsegmentation principles
- Use secure tunnels with strict ACLs
- Implement east-west traffic controls
Secure CI/CD
- Scan dependencies and sign artifacts
- Use reproducible builds
- Implement security gates in pipelines
Sample IAM Least-Privilege Role
{ "Version": "2012-10-17", "Statement": [ { "Effect": "Allow", "Action": [ "s3:GetObject", "s3:ListBucket" ], "Resource": [ "arn:aws:s3:::example-prod-bucket", "arn:aws:s3:::example-prod-bucket/*" ] } ]
}
Incident Preparedness and Response: Playbooks, Tabletop Exercises, and Cross-Domain Coordination
Prepare for incidents with practiced playbooks:
- Maintain hybrid incident response plans that include cloud provider contacts and access procedures.
- Run regular tabletop exercises that simulate data exfiltration, compromised CI/CD, or ransomware.
- Coordinate across cloud, network, application, legal, and communications teams.
Operational tip: Build API calls or automation to quickly revoke cloud credentials or rotate keys during containment phases of incident response.
Preparing for the Future of Mixed cloud environment Security

Figure 6: Future of hybrid infrastructure security: evolving threats and strategic investments
Anticipated Evolution of Combined cloud Security Threats and Attacker Tactics
Expect attackers to:
- Exploit advanced automation and AI to find misconfigurations faster
- Target supply chains and CI/CD pipelines more aggressively
- Focus on identity compromise and service token theft
Defenders must proactively reduce attack surface and improve detection of subtle behavioral anomalies in hybrid environments.
Strategic Investments: Tooling, Talent, Partnerships, and Supplier Risk Management
Prioritize investments that deliver resilient hybrid cloud security:
| Investment Area | Priority Actions | Expected Outcomes |
| Tooling | Deploy CSPM, workload protection, and SIEM with cloud telemetry | Improved visibility, automated detection, reduced response time |
| Talent | Invest in cloud security training and certifications | Enhanced capability to secure complex environments |
| Partnerships | Engage MSSPs or CSP partners to augment capabilities | Access to specialized expertise and 24/7 coverage |
| Supplier Risk | Vet third-party dependencies and include security SLAs | Reduced supply chain risk and improved vendor accountability |
Roadmap for Resilience: Integrating Cloud Security Trends into Long-Term Hybrid setup Risk Management
Create a multi-year roadmap for mixed cloud environment security:
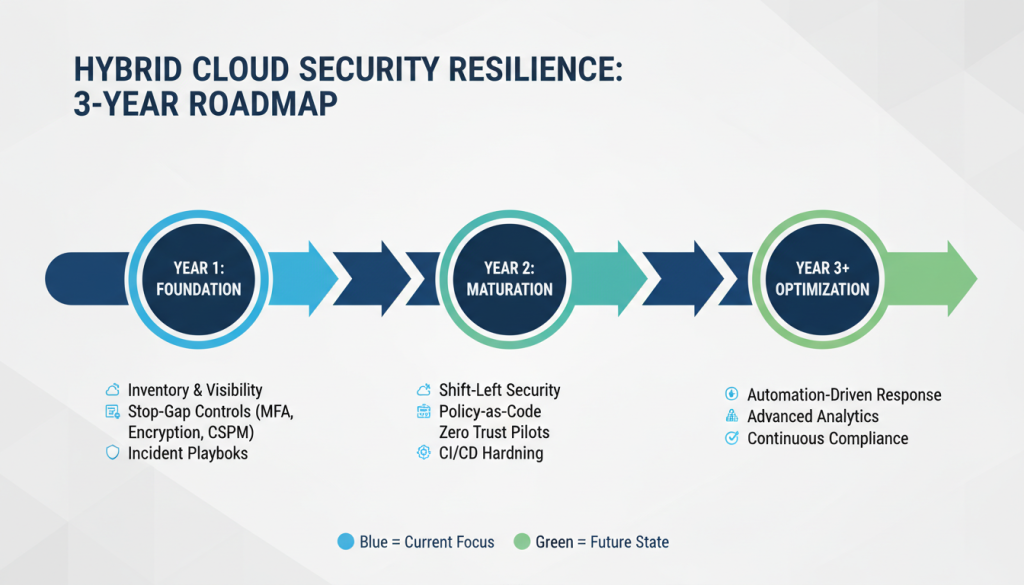
Figure 7: Multi-year roadmap for hybrid infrastructure security resilience
- Year 1: Inventory, visibility, stop-gap controls (MFA, encryption, CSPM), and incident playbooks.
- Year 2: Shift-left, policy-as-code, zero trust pilots, and CI/CD hardening.
- Year 3+: Full operationalization of automation-driven response, advanced analytics, and continuous compliance.
Embed continuous threat landscape analysis to adapt the roadmap as cloud security trends evolve.
Conclusion
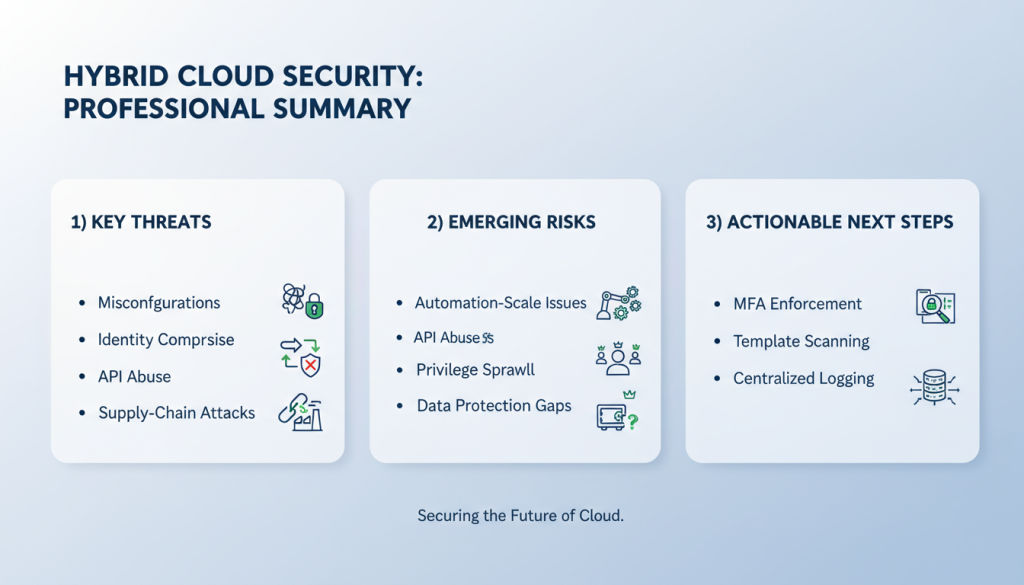
Figure 8: Summary of key hybrid cloud security threats, risks, and mitigation strategies
Recap of Key Mixed cloud environment Security Threats, Emerging Security Risks, and Cloud Security Challenges
Hybrid cloud security threats range from misconfigurations and identity compromise to API abuse and supply-chain attacks. Emerging security risks specific to hybrid environments include automation-scale misconfigurations, privilege sprawl, and data protection gaps. Operational cloud security challenges — visibility, compliance, and people/process issues — magnify these risks.
Actionable Next Steps: Immediate Mitigations, Monitoring Priorities, and Strategic Planning
Immediate Mitigations
- Enforce MFA and least-privilege IAM
- Scan and remediate IaC templates
- Centralize logging with CSPM/CWPP
Monitoring Priorities
- Detect anomalous identity behavior
- Monitor for data exfiltration patterns
- Track configuration drift
Strategic Planning
- Implement Zero Trust principles
- Invest in cloud security training
- Prepare incident response playbooks
Final Thoughts on the Future of Hybrid Cloud Security
The future of hybrid cloud security will be defined by how quickly organizations can integrate security into development and operations while maintaining control over identity and data. Embrace automation, adopt identity-first defenses, and prioritize continuous risk assessment. By aligning tooling, people, and processes — and leaning into emerging cloud security trends — organizations can reduce risk and stay ahead of adversaries in a rapidly changing threat landscape.
Start with a focused threat landscape analysis this quarter — inventory cloud assets, identify the top 3 high-impact misconfigurations or identity weaknesses, and run a tabletop exercise to validate your incident response readiness.
Strengthen Your Hybrid Cloud Security Posture
Download our comprehensive Hybrid Cloud Security Checklist with actionable steps to protect your environment against emerging threats.
